Networking of machines/Machine-to-Machine (M2M)
Machine-to-Machine (M2M) describes the automated flow of information between end devices such as production machines, control units, automats or vehicles and thus simplifies work processes. Networking is increasingly taking place via the internet, which also makes remote monitoring possible. This streamlining of business processes and the resulting cost savings offer great potential for companies.
An M2M application usually consists of three components. The first component is the data endpoint (DEP), for example a production machine. This passes on information via the second component, the communication network (LTE, 5G) to the third component, the data integration point (DIP). This monitors all data and helps interpret events. In most applications, there is one DIP, while there can be several DEPs communicating with each other.
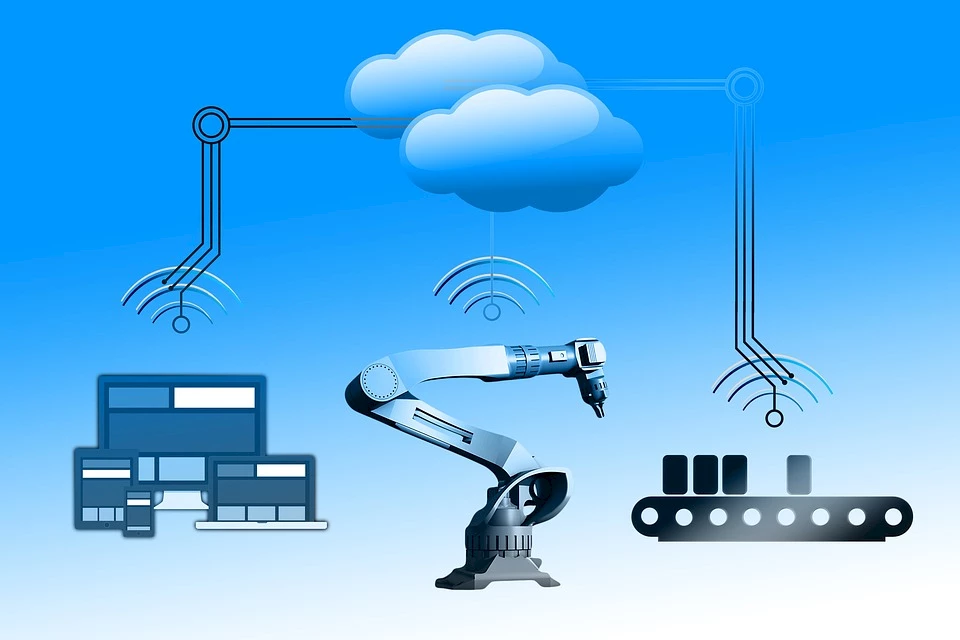 Networking of the machines
Networking of the machines© https://pixabay.com/de/photos/industrie-industrie-4-netz-netzwerk-2738405/
Requirements for use
Stable internet connection
The microcontrollers embedded in the machine use the Internet together with a specific protocol language to ensure data exchange. If the connection is interrupted, they cannot follow the data exchange in real time.
Data security
The greater the number of machines communicating with each other, the more vulnerable the network is to cyber attacks. Therefore, sensitive handling of data and an inherently secure network are basic requirements for the use of M2M communications.
